Liquid Damage Repair: Your Ultimate Solution at Our Service Centre

Liquid Damage Repair: Your Ultimate Solution at Our Service Centre
Liquid damage to your electronic devices can be a devastating experience, leaving you with a malfunctioning tablet or laptop. Whether it’s a spilled cup of coffee, an accidental dip in the pool, or a rain-soaked backpack, liquid can wreak your valuable devices. Fortunately, our service center is here to provide you with top-notch liquid damage repair services that can revive your devices and save you from the hassle and cost of replacing them.
Why Choose Our Liquid Damage Repair Service Centre?
Experienced Technicians:
Our team of highly skilled technicians has years of experience in handling liquid-damaged devices. They have successfully repaired numerous devices, from tablets to laptops. Rest assured that your device is in capable hands.
Advanced Equipment:
We invest in the latest and most advanced equipment to diagnose and repair liquid-damaged devices efficiently. Our tools help us identify the extent of the damage and perform precise repairs, minimizing the risk of further issues down the line.
Quick Turnaround:
We understand the importance of your devices in your daily life, so we strive to provide a quick repair for liquid damage repair. In most cases, we can have your device back to you in working order within a matter of days.
Affordable Pricing:
We believe that quality repairs shouldn’t break the bank. Our liquid damage repair services are competitively priced, making it a cost-effective alternative to replacing your device.
Comprehensive Solutions:
Whether your device is suffering from water damage, coffee spills, or any other liquid-related, our service center offers comprehensive solutions. We can repair damaged components, clean internal parts, and ensure your device functions like new ones.
When faced with liquid damage to your valuable devices, don’t panic. Our service center is your trusted partner in expert liquid damage repair. With experienced technicians, advanced equipment, competitive pricing, and a commitment to quality, we’re here to get your device back in your hands, fully functional. Say goodbye to the stress of liquid damage and trust us for reliable repairs that make your device feel like new.
Fresh Start for Devices: Optimal Performance Tips

Give Your Devices a Fresh Start: Tips for Optimal Performance
In today’s digital age, our lives revolve around technology and devices. From laptops to tablets and smart TVs, these devices play a crucial role in our daily tasks, communication, and entertainment. However, our devices can benefit from a fresh start every now and then.
1. Clean Up Your Device:
Over time, our devices accumulate unnecessary files, apps, and data that can slow down their performance. Take the time to clean your device by deleting old and unused apps, clearing cached files, and organizing your data. This will not only free up valuable storage space but also improve your device’s speed and responsiveness.
2. Update Software and Firmware:
Regular software and firmware updates are essential to keep your devices running smoothly and securely. Manufacturers often release updates to fix bugs, enhance performance, and introduce new features. Make it a habit to check for updates and install them promptly to ensure your device is up to date.
3. Reset Factory Settings:
If you’re experiencing persistent issues or slowdowns, consider performing a factory reset. This process restores your device to its original settings, effectively wiping out all data and apps. Remember to back up your important data before proceeding with a reset. After the reset, your device will feel like new, but be sure to reinstall only the apps you truly need to prevent clutter from building up again.
4. Optimize Storage:
Running low on storage can significantly impact your device’s performance. Regularly review your storage and delete large files or move them to cloud storage solutions. Additionally, enable automatic backup options for photos and other media to free up space without losing important memories.
5. Clear Browser Cache:
If you use your device for browsing the internet, your browser’s cache can accumulate over time, leading to slower loading times and potential security issues. Clearing your browser’s cache and cookies periodically can help improve browsing speed and protect your privacy.
6. Protect Against Malware:
Malicious software can severely compromise your device’s performance and security. Install reputable antivirus and antimalware software to safeguard your device from potential threats. Regular scans and real-time protection can prevent malware from causing harm.
7. Monitor Battery Health:
For devices with rechargeable batteries, keeping an eye on battery health is crucial. Over time, batteries degrade, leading to decreased performance and shorter battery life. Some devices offer battery health monitoring tools that allow you to assess your battery’s condition and take appropriate actions.
8. Consider Hardware Upgrades:
If your device’s performance is consistently lagging behind your needs, consider upgrading specific hardware components. For example, upgrading your device’s RAM or storage can significantly boost its performance and extend its lifespan.
Our gadgets are useful tools that improve our lives in many ways, but in order to function at their peak, they need upkeep and attention. You may get the best performance, increased speed, and a better user experience by using these suggestions for giving your devices a new start. Keep in mind that routine maintenance can greatly increase the lifespan of your gadgets and ensure that they continue to serve your needs in the constantly changing world of technology.
Exploring Acer Aspire Laptops: A Comprehensive Guide

Exploring Acer Aspire Laptops: A Comprehensive Guide
Acer’s Aspire series has long been recognized for delivering a diverse range of laptops catering to different user needs. Whether you’re a student, a professional, a content creator, or a casual user, Acer Aspire laptops offer a variety of models and configurations to suit your requirements. In this comprehensive guide, we’ll delve into the key aspects that make Acer Aspire laptops stand out, from design and performance to features and affordability.
Design and Build Quality:
Acer Aspire laptops feature a combination of sleek designs and robust build quality. The design aesthetics vary from slim and modern to more rugged builds for specific use cases. The series often incorporates metal or high-quality plastic chassis, providing durability and a premium feel.
Performance Options:
Acer Aspire laptops offer a wide range of performance options, accommodating both casual users and power-hungry professionals. Depending on the model, you can find Intel Core, AMD Ryzen, or even dedicated NVIDIA or AMD graphics for enhanced gaming and content creation capabilities.
Display Varieties:
The series includes laptops with a diverse array of display options, including Full HD and even 4K panels. Some models also offer touchscreen functionality, providing a more interactive experience for users who prefer it.
Connectivity and Ports:
Acer equips its Aspire laptops with a selection of ports for versatile connectivity. USB Type-A, USB Type-C, HDMI, and SD card slots are commonly found across the series, ensuring compatibility with various peripherals and external devices.
Battery Life:
Battery life varies based on the specific model and its usage, but many Acer Aspire laptops offer decent battery life for a full day’s work or entertainment. It’s essential to consider battery capacity and efficiency when choosing a laptop.
Specialized Models:
Acer Aspire lineup also includes specialized models tailored to specific tasks. For instance, Aspire Swift focuses on ultraportability, Aspire Nitro targets gaming enthusiasts, and Aspire Spin offers 2-in-1 convertible functionality for versatile usage modes.
Software Enhancements:
Some Acer Aspire laptops come with proprietary software enhancements like Acer TrueHarmony for enhanced audio quality, Acer Color Intelligence for improved display visuals, and Acer CoolBoost for managing system cooling.
Affordability:
One of the standout features of Acer Aspire laptops is their affordability. The series provides a cost-effective solution without compromising too much on performance or features, making it an attractive option for budget-conscious consumers.
Customer Support and Warranty:
Acer typically offers standard warranty options and customer support for its Aspire laptops. It’s important to research the warranty terms and available support channels before making a purchase.
Acer Aspire laptops have consistently provided a range of options that balance design, performance, features, and affordability. With a diverse lineup catering to various user needs, the Aspire series remains a popular choice for individuals seeking reliable computing devices. By considering factors such as design, performance, display options, and specialized models, you can find an Acer Aspire laptop that aligns perfectly with your requirements and preferences.
Strengthening Cybersecurity: Newtech & Underdefense Partnership

New Partnership between Newtech and Underdefense – Strengthening Cybersecurity
We’re thrilled to announce our incredible partnership with UnderDefense!
We’re excited to announce our incredible partnership with UnderDefense, aimed at Strengthening Cybersecurity!
UnderDefense, a renowned leader in cybersecurity solutions, and us are joining forces to enhance our capabilities in safeguarding businesses and individuals from evolving cyber threats.
With their expertise and our innovative technologies, we’re committed to providing unparalleled protection and peace of mind to our valued clients.
UnderDefense cybersecurity services include:
- Conducting security assessments and penetration testing: UnderDefense identifies vulnerabilities by analyzing the network infrastructure, applications, and systems within an organization. Testing vulnerabilities simulates real-world attacks and evaluates existing security measures.
- Providing managed security services: Additionally, UnderDefense monitors and manages an organization’s security infrastructure. This includes 24/7 threat detection, incident response, log analysis, vulnerability management, and firewall management.
- Offering incident response services: In the event of a cybersecurity incident, UnderDefense provides services to minimize the impact and recover from the incident. This may involve forensic analysis, containment, eradication of threats, and implementing measures to prevent future incidents.
- Providing security consulting and advisory services: Furthermore, UnderDefense offers expert advice and guidance to organizations on their cybersecurity strategy, risk management, compliance, and regulatory requirements. They help organizations develop and implement effective security policies, procedures, and controls.
- Offering threat intelligence services: Moreover, UnderDefense provides threat intelligence services to help organizations stay informed about the latest cyber threats and vulnerabilities. They offer real-time threat intelligence feeds, reports, and analysis, enabling organizations to proactively defend against emerging threats.
- Conducting security awareness training programs: Lastly, UnderDefense conducts cybersecurity awareness training programs for employees. This helps educate them about potential risks, best practices, and how to identify and respond to security incidents, creating a security-conscious culture and minimizing human-related vulnerabilities.
It’s important to note that UnderDefense’s specific services may vary. We recommend visiting their official website or contacting them directly for the most up-to-date and accurate information.
Laptop Damage Prevention

How to Avoid Common Laptop Damage
Laptop Damage Prevention: How to Safeguard Your Device
Laptops have become indispensable in our daily lives, whether for work, education, or entertainment. However, without proper care, they are susceptible to various forms of damage. In this guide, we’ll explore effective strategies for laptop damage prevention to ensure your device remains in optimal condition for the long haul.
Invest in Protective Measures:
To safeguard your laptop from physical harm, consider investing in a sturdy protective case or sleeve. These accessories provide an extra layer of defense against accidental drops, bumps, and scratches, significantly reducing the risk of damage.
Handle with Care:
When transporting your laptop, always handle it with care, using both hands to support its weight. Avoid carrying it by the screen or leaving it open while in transit, as these actions can increase the likelihood of damage.
Shield Against Liquid Exposure:
One of the most common causes of laptop damage is liquid spills. To prevent this, ensure all liquids are kept far away from your device at all times. Implementing strict rules against drinking near your laptop can help mitigate the risk of accidental spills and potential irreparable damage.
Prevent Overheating:
Overheating can pose a significant threat to your laptop’s internal components. To prevent this, invest in a quality cooling pad to help dissipate heat during prolonged use. Additionally, make it a habit to regularly clean the air vents and fan to remove dust and debris, ensuring optimal airflow and preventing overheating.
Protect Against Power-Related Issues:
Power surges can wreak havoc on your laptop’s delicate electronics. To safeguard against this, use surge protectors when charging your device. Furthermore, always unplug the power cord by gripping the plug firmly, rather than pulling on the cord itself, to avoid potential damage.
Software and Data Security:
Keeping your laptop’s software and data secure is essential for preventing potential damage. Ensure your operating system, antivirus software, and other programs are regularly updated to patch security vulnerabilities. Additionally, regularly back up your important files to external storage or the cloud to mitigate the risk of data loss in the event of hardware failure or a malware attack.
Maintain Keyboard and Screen Integrity:
Proper maintenance of your laptop’s keyboard and screen is crucial for preventing damage. Use a can of compressed air or a soft brush to remove dust and debris from the keyboard, avoiding the use of excessive force or liquids. When closing the laptop lid, do so gently to prevent pressure or objects from damaging the screen. Consider investing in a screen protector to minimize the risk of scratches and other forms of damage.
By implementing these proactive measures for laptop damage prevention, you can significantly prolong the lifespan of your device and ensure it continues to perform optimally for years to come. Remember, prevention is always preferable to repair, so invest the time and effort now to safeguard your laptop against future damage and avoid costly repairs or replacements down the line.
7 Laptop Cleaning Tips for Peak Performance

Laptop Cleaning Tips for Maintenance and Longevity
Regularly Clean the Laptop Exterior
Laptop Cleaning Tips – It is essential for your laptop to be clean for its durability and optimal performance. Dust, dirt, and smudges can accumulate on your laptop’s surface and affect its functionality. We will provide you with seven practical tips to keep your laptop clean and well-maintained.
Keep the Keyboard Clean
The keyboard is prone to dirt and dust accumulation. Power down your laptop and use compressed air to dislodge any debris or crumbs nestled between the keys. For stubborn stains, a cotton swab dipped in isopropyl alcohol can help gently cleanse affected areas.
Utilize a Screen Cleaning Solution
Maintaining a spotless screen is crucial for optimal viewing. Power off your laptop and apply a small amount of screen cleaning solution to a microfiber cloth. Gently wipe the screen in circular motions, avoiding abrasive materials that could scratch its surface.
Ensure Adequate Ventilation
Proper airflow is essential for your laptop’s functionality and longevity. Regularly inspect and clear ventilation ports and fans of dust and debris using compressed air. Focus on areas around vents and fans to prevent overheating and sustain peak performance.
Avoid Food and Liquid Proximity
Protect your laptop from accidental spills and crumbs by establishing a strict no-food-and-drink policy while using it. This simple precaution can help preserve its cleanliness and safeguard against potential damage.
Optimal Storage and Transportation
Shield your laptop from scratches, dust, and impacts by storing it in a dedicated case or sleeve when not in use. During transport, employ a padded bag or backpack designed for laptops to mitigate the risk of damage.
Implement Routine Software Maintenance
Elevate your maintenance routine beyond physical cleaning by ensuring your software is up to date. Regularly update your operating system and antivirus software, remove unnecessary programs and files, and run disk cleanup and defragmentation utilities to optimize performance and security.
By adhering to these laptop cleaning tips, you can uphold the cleanliness, functionality, and longevity of your device. From meticulous exterior care to diligent software maintenance, these practices are essential for preserving your laptop’s performance for years to come.
https://newtech.mt/service-centers-repairs/
Authorized Service Centre for Lenovo, Acer, and MSI
Providing Reliable Service:
Authorized Service Center for Lenovo, Acer, and MSI
In today’s world, having access to reliable and efficient service centers is crucial for customers who encounter issues with their electronic devices. We are proud to announce that our service center has earned the prestigious status of being an authorized service center for three leading technology brands: Lenovo, Acer, and MSI. This achievement reflects our commitment to providing high-quality repair and maintenance services to our valued customers.
Expertise and Accreditation
Becoming an authorized service center involves strict requirements and demonstrating expertise in handling products from these renowned brands. Firstly, we have gone through a strict evaluation process, ensuring that we have the necessary technical knowledge, infrastructure, and genuine spare parts to offer quality service.
Moreover, our team of highly trained technicians possesses in-depth knowledge about Lenovo, Acer, and MSI devices. Whether it’s a malfunctioning laptop, a tablet with a cracked screen, or a gaming PC in need of an upgrade, we have the expertise to diagnose and resolve issues efficiently. Our technicians stay up to date with the latest product developments, furthermore, troubleshooting techniques, and repair methodologies through continuous training provided by the manufacturers.
Skilled Technicians and Continuous Training
Our team of highly trained technicians possesses in-depth knowledge about Lenovo, Acer, and MSI devices. Whether it’s a malfunctioning laptop, a tablet with a cracked screen, or a gaming PC in need of an upgrade, we have the expertise to diagnose and resolve issues efficiently. Our technicians stay up to date with the latest product developments, troubleshooting techniques, and repair methodologies through continuous training provided by the manufacturers.
Access to Official Tools and Genuine Parts
Additionally, as an authorized service center, we have access to official repair tools, diagnostic software, and genuine parts provided directly by Lenovo, Acer, and MSI. This ensures that we can perform repairs and replacements using original components, maintaining the integrity and performance of the devices.
Warranty Support and Customer Satisfaction
Customers who bring their Lenovo, Acer, and MSI products to our service center can enjoy the benefits of warranty support. We handle warranty claims efficiently, furthermore, we stick to the manufacturers’ guidelines and processes. Consequently, with our authorized status, customers can have peace of mind knowing that their devices are being serviced by professionals who understand the intricacies of the products.
Transparent Service and Trust
Our focus is customer satisfaction. Therefore, we strive to provide a smooth experience to our customers, ensuring prompt service, clear communication, and transparent pricing. By offering authorized service, we instill trust in our customers, thus assuring them that their devices are in capable hands and will be repaired to the highest standards.
Exceptional Service for Lenovo, Acer, and MSI Customers
As an authorized service center for Lenovo, Acer, and MSI, we are committed to delivering reliable, efficient, and professional repair services. Our expertise gives us access to official tools and genuine parts, and our loyalty to warranty support guidelines set us apart from unauthorized service providers.
We invite Lenovo, Acer, and MSI customers to experience our exceptional service and trust us with their valuable devices.
Explore the Unknown - Password Guide
Tips For Password Security
The guidelines and steps for creating strong and secure passwords.
- Keep your passwords private – never share a password with anyone else
- Do not write down your passwords, use a password manager instead
- Use passwords of at least eight (8) characters or more (longer is better)
- Use a combination of upper case letters, lower case letters, numbers, and special characters (for example: !, @, &, %, +) in all passwords
- Avoid using people’s or pet’s names, or words found in the dictionary; it’s also best to avoid using key dates (birthdays, anniversaries, etc.)
- Substituting look-alike characters for letters or numbers is no longer sufficient (for example, Password” and “P@ssw0rd”)
- A strong password should look like a series of random characters
How To Create A Strong, Complex Password
Here’s a way to make a strong password that’s very hard to crack:
FOLLOW THESE STEPS
- Think of a phrase or sentence with at least eight words. It should be something easy for you to remember but hard for someone who knows you to guess. It could be a line from a favorite poem, story, movie, song lyric, or quotation you like.
Example:
I Want To Put A Dent In The Universe
- Remove all but the first letter of each word in your phrase.
IWTPADITU
- Replace several of the upper-case letters with lower case ones, at random.
iWtpADitU
- Now substitute a number for at least one of the letters. (Here, we’ve changed the capital “I” to the numeral 1).
iWtpAD1tU
- Finally, use special characters ( $, &, +, !, @) to replace a letter or two — preferably a letter that is repeated in the phrase. You can also add an extra character to the mix. (Here, we’ve replaced the “t” with “+”, and added an exclamation point at the end.)
iW+pAD1tU!
Why This Is Important ?
Traditional passwords can be cracked by hackers in less than a minute! Follow this guide to create passwords that would take centuries to crack.

Email Vigilance Checklist: Safeguarding Your Inbox
Email Vigilance Checklist: Safeguarding Your Inbox
In today’s digital age, email has become an indispensable tool for communication in both personal and professional spheres. However, with the convenience of email also comes the risk of cyber threats such as phishing, malware, and spoofing. To protect yourself and your organization from these dangers, it’s crucial to adopt robust email security practices. Here are some essential tips to help you safeguard your inbox:
Validate Sender Information:
Always scrutinize the ‘from’ field of an email to verify the sender’s identity. Keep in mind that malicious actors can easily spoof email addresses to deceive recipients. If an email seems suspicious or unexpected, double-check the sender’s details before taking any further action.
Exercise Caution with Attachments:
Be cautious when opening email attachments, particularly those with executable file extensions such as ‘.exe’. A general rule of thumb is to avoid opening attachments from unknown or untrusted sources. Additionally, be wary of files with double extensions (e.g., ‘safe.txt.exe’), as they could contain harmful malware.
Report Suspicious Activity:
If you receive an email that raises suspicions or appears to be a phishing attempt, report it immediately to your organization’s IT help desk or security team. Prompt reporting can help prevent potential security breaches and protect other users within your organization.
Verify Hyperlinks:
Before clicking on any hyperlinks embedded in an email, hover your mouse cursor over the link to preview the URL. Watch out for discrepancies between the displayed URL and the actual destination. Be especially cautious of hyperlinks that lead to unfamiliar or suspicious websites, as they could be phishing sites designed to steal your personal information.
Stay Vigilant Against Domain Spoofing:
Cybercriminals often use domain spoofing techniques to create fraudulent websites that mimic legitimate ones. Pay close attention to the domain name in email links and be wary of subtle variations or misspellings. For example, ‘www.bankofarnerica.com‘ may appear similar to the legitimate ‘www.bankofamerica.com‘, but it could lead to a malicious site.
By adhering to these email security best practices, you can significantly reduce the risk of falling victim to cyber threats and protect your sensitive information. Remember, maintaining a vigilant and cautious approach to email communication is key to safeguarding both your personal and professional digital assets.
If you have any further questions or concerns about email security, don’t hesitate to reach out to your organization’s IT support team for assistance. Stay safe, stay secure!

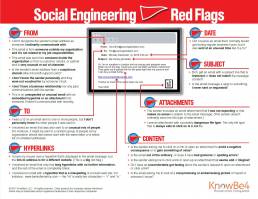
Red Flags - Stay Alert and Stay Safe
Red Flags – Social Engineering
Identify Red Flags in an Email
Identifying red flags in an email is crucial to stay alert and stay safe from social engineering attacks. Here’s a breakdown of what to look out for:
Stay Alert: Red Flags From the Sender:
- First and foremost, check if the sender’s email address is unfamiliar or unrelated to your usual contacts.
- Additionally, scrutinize whether the email is from someone outside your organization, not related to your job responsibilities.
- Equally important is to assess if the email is from someone inside your organization, but the content is unusual or out of character.
- Furthermore, watch out for suspicious sender email domains, like “micorsoft support.com.”
- Moreover, consider if there’s a lack of personal acquaintance or endorsement from someone you trust.
- Take note if there’s no prior business relationship or communication history with the sender.
- Lastly, be wary of unexpected or unusual content, especially with embedded hyperlinks or attachments.
Stay Safe: Spotting Suspicious Hyperlinks:
- It’s important to mention that hovering over a hyperlink reveals a different destination URL, a significant red flag.
- Another key point is that emails with only long hyperlinks and no further context or content are suspicious.
- Additionally, be cautious of misspelled hyperlinks mimicking known websites, such as “www.bankofarnerica.com.”
Stay Vigilant: Identifying Unusual Recipients and Attachments:
- Consider whether you’ve been cc’d on an email to unfamiliar recipients.
- Additionally, be cautious of emails sent to an unusual mix of people, such as random groups or unrelated addresses.
- Look out for unexpected or nonsensical attachments, especially from senders who don’t typically send such files.
- Also, be cautious of attachments with potentially dangerous file types, with .txt files being the only inherently safe type.
Stay Aware: Timing, Subject Lines, and Content:
- It’s worth noting if emails are received at unusual times, especially outside regular business hours.
- Take note of irrelevant subject lines or subject lines that don’t match the email content.
- Similarly, be cautious of emails that appear as replies to unrequested or unsent messages.
- Pay attention to requests to click on links or open attachments under the threat of negative consequences or with promises of gain.
- Also, watch out for unusual or poor grammar and spelling errors in the email.
- Additionally, consider whether there are illogical or suspicious requests to click on links or open attachments.
- Trust your instincts if you sense discomfort or suspicion regarding the email’s content.
- Lastly, be cautious of emails requesting viewing of compromising or embarrassing images.
By being vigilant and attentive to these red flags, you can protect yourself and your organization from falling victim to social engineering attacks.